If you run a Canadian tech company with 10 to 150 employees, you've probably heard the question: "Do you have SOC 2?"
It usually comes from an enterprise prospect, a partner doing vendor due diligence, or an insurance provider tightening their requirements. And it usually comes at the worst possible time — right when a deal is on the line.
SOC 2 is becoming the cost of doing business for Canadian software companies. But most of the information out there is written for American companies, by American vendors, assuming American infrastructure. This post is for Canadian founders who need to understand what SOC 2 actually requires, what it costs, and how to approach it without spending six figures on consultants.
What SOC 2 actually is
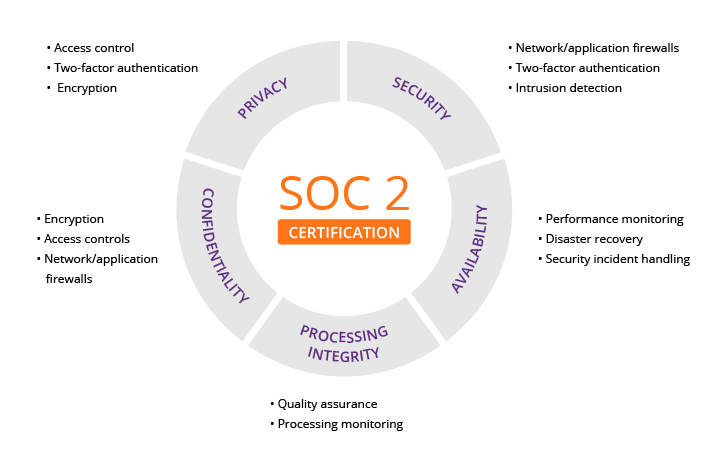
SOC 2 is a security framework developed by the American Institute of Certified Public Accountants (AICPA). It evaluates how a company protects customer data across five categories called Trust Service Criteria: security, availability, processing integrity, confidentiality, and privacy.
There are two types. Type I is a snapshot — it confirms your controls are designed properly at a single point in time. Type II is the real one — it confirms your controls are working effectively over a period of time, usually 6 to 12 months.
Most enterprise buyers and partners want Type II. A Type I report can get you through early conversations, but it won't satisfy a serious procurement team for long.
Why Canadian companies are getting asked for it
Three forces are pushing SOC 2 adoption across Canada.
Enterprise sales requirements. If you sell software to mid-market or enterprise companies, their security teams will ask for your SOC 2 report during vendor evaluation. No report often means no deal. This is especially true if you're selling into financial services, healthcare, education, or government-adjacent sectors.
Cyber insurance. Insurance providers in Canada are tightening their underwriting requirements. Having SOC 2 — or at least demonstrating you're working toward it — can meaningfully reduce your premiums and improve your ability to get coverage at all.
Canadian privacy law. PIPEDA at the federal level and provincial laws like Quebec's Law 25 and BC's PIPA create obligations around how you handle personal information. SOC 2's privacy and confidentiality criteria overlap significantly with these requirements. Achieving SOC 2 doesn't replace PIPEDA compliance, but the controls you build for one often satisfy the other. At VimyHQ, we map SOC 2 controls directly to PIPEDA and Law 25 requirements so you can track compliance across multiple frameworks from a single platform.
What SOC 2 actually requires from a small team
This is where most founders get overwhelmed. SOC 2 sounds like it requires an army of compliance professionals. It doesn't. But it does require discipline across several areas.
Access controls. Who can access what, and how do you prove it? This means role-based access to your production systems, mandatory multi-factor authentication, regular access reviews, and documented onboarding and offboarding procedures. VimyHQ's Identity Battery monitors your Google Workspace and identity providers continuously, flagging MFA gaps, over-permissioned accounts, and suspicious OAuth grants — all of which map directly to SOC 2 access control requirements.
Monitoring and logging. You need to demonstrate that you're watching for security events — failed logins, privilege escalations, configuration changes, unusual access patterns. You also need to show that you retain logs and review them. This is where most small teams fall short — not because they don't care, but because manual log review doesn't scale. Automated security monitoring solves this by turning raw events into actionable intelligence and generating the compliance evidence your auditor needs.
Incident response. You need a documented plan for what happens when something goes wrong. Who gets notified, how do you contain the issue, how do you communicate with affected customers, and how do you learn from it afterward. VimyHQ generates incident narratives automatically — a technical timeline for your IT team, a business impact summary for leadership, and a compliance artifact for your auditor. One incident, three outputs, zero manual writing.
Vendor management. If you use third-party services that touch customer data, you need to evaluate their security posture. This includes your cloud provider, your email platform, your payment processor — anyone in the chain.
Change management. How do you deploy code? Is it reviewed before it goes to production? Do you have a process for testing, approving, and rolling back changes?
Encryption. Data at rest and in transit should be encrypted. For Canadian companies, this also raises the question of where your data is physically stored and processed — a question that matters more here than most founders realize.
The data sovereignty question
Here's where Canadian companies face a challenge that American ones don't.
Most compliance automation platforms on the market — Drata, Vanta, Sprinto, Secureframe — are American companies that store and process data on American infrastructure. When you use these tools, your compliance evidence, employee data, security configurations, and audit artifacts are sitting on servers in the United States, subject to American law.
For many Canadian companies, this creates a contradiction: you're trying to demonstrate security and privacy compliance while sending sensitive data to a foreign jurisdiction. Under PIPEDA and provincial privacy laws, organizations are accountable for the personal information they transfer to third parties — including cross-border transfers.
This is exactly why we built VimyHQ on 100% Canadian infrastructure. Every byte of data — security events, compliance evidence, AI processing — stays in Canada on DigitalOcean's Toronto data center. Zero US subprocessors. No cross-border transfers. Your compliance data stays under Canadian law, full stop.
This doesn't mean you can't use American tools. But it does mean you should understand what you're agreeing to and whether your customers or regulators will care. For companies in healthcare, financial services, or government-adjacent sectors, this is increasingly a dealbreaker.
What SOC 2 doesn't require
It's worth addressing what SOC 2 does not demand, because there are common misconceptions.
It doesn't require specific tools. SOC 2 is framework-agnostic. You don't need a specific endpoint protection vendor, a specific cloud provider, or a specific compliance platform. You need to demonstrate that your controls are effective, regardless of the tools you use.
It doesn't require perfection. SOC 2 auditors are looking for evidence that your controls work consistently, not that nothing ever goes wrong. An incident that was detected, contained, and documented properly can actually demonstrate the strength of your program.
It doesn't require a massive team. Companies with 10 to 20 employees achieve SOC 2 regularly. The key is having clear ownership of each control area and the discipline to document what you do.
It doesn't require you to do everything at once. You can start with the Security criterion alone (this is the most common starting point) and add Availability, Confidentiality, or Privacy criteria later as your program matures.
The real cost breakdown
The cost of SOC 2 varies widely depending on how you approach it.
Compliance consultants typically charge $60,000 to $120,000 or more to guide you through the process, help you build policies, and prepare for audit. For a 20-person company, this is often the single largest line item.
The audit itself (conducted by a licensed CPA firm) runs $20,000 to $50,000 for Type II, depending on scope and complexity.
Compliance automation platforms range from $10,000 to $30,000 per year. These platforms help you collect evidence, monitor controls, and stay audit-ready — reducing (but not eliminating) the need for consultants. VimyHQ's Bastion plan starts significantly below this range while including real-time security monitoring alongside compliance automation — something most compliance-only tools don't offer.
Internal time is the cost most people forget. Someone on your team needs to own the compliance program. At a small company, this is often the CTO or a senior engineer who spends 10 to 20 hours per week on it during the preparation phase.
The total cost for a first-time SOC 2 Type II at a 20 to 50 person Canadian company typically lands between $40,000 and $150,000 in the first year. The range is wide because the approach matters enormously.
A practical path forward
If you're a Canadian tech company preparing for SOC 2, here's a realistic sequence.
Month 1 to 2: Assess your current state. Before you hire anyone or buy anything, understand where you stand. Audit your access controls, review your logging, document your current processes. You'll likely find that you're already doing 30 to 40 percent of what SOC 2 requires — you're just not documenting it.
Month 2 to 3: Close the gaps. Focus on the areas where you have no controls at all. Common gaps for Canadian startups include formal access reviews, documented incident response plans, vendor security assessments, and change management procedures.
Month 3 to 6: Build evidence. SOC 2 Type II requires evidence over time. Start collecting it now — access review records, log monitoring reports, incident response documentation, change management approvals. The longer your evidence period, the stronger your audit. This is where a platform like VimyHQ pays for itself — your security operations generate compliance evidence automatically as a byproduct of real protection, so you're not scrambling to build documentation at audit time.
Month 6 to 9: Engage an auditor. Choose a CPA firm experienced with technology companies. Canadian firms like KPMG, MNP, and Richter handle SOC 2 audits, as do specialized firms like Prescient Assurance and Johanson Group.
Month 9 to 12: Complete the audit and receive your report. A clean Type II report is valid for 12 months. After that, you renew annually — which is significantly less work than the first time.
The bottom line
SOC 2 is not optional for Canadian tech companies that want to sell to enterprises, secure cyber insurance, or demonstrate compliance with Canadian privacy law. It's also not as overwhelming as the consulting industry wants you to believe.
The companies that do it well are the ones that treat compliance as an ongoing part of how they operate — not a one-time project they throw money at. When your security operations are solid, compliance evidence becomes a byproduct, not a burden.
That's the approach we built VimyHQ around. Real security operations — threat detection, identity monitoring, infrastructure protection — that automatically generate the compliance artifacts you need for SOC 2, PIPEDA, ISO 27001, and cyber insurance. All on 100% Canadian infrastructure, with zero US subprocessors.
If your enterprise customers are starting to ask about SOC 2, the best time to start preparing was six months ago. The second best time is now. Talk to us and we'll show you exactly where you stand.
VimyHQ is a cybersecurity and compliance automation platform built on Canadian infrastructure for Canadian companies. Learn more · See our plans · Book a demo