SOC 2 compliance that builds itself.
Vimy maps controls across all five Trust Services Criteria and auto-collects evidence from your live security operations. No screenshots. No spreadsheets. No audit prep sprints.
SOC 2 shouldn't take 6 months and a consultant.
Your enterprise prospects want SOC 2. Your auditor wants evidence. Your team wants to ship product, not collect screenshots.
Traditional SOC 2 prep means hiring a consultant, buying a compliance tool, spending months mapping controls, manually collecting evidence, and then doing it all again next year. It's expensive, slow, and disconnected from your actual security.
Manual evidence collection
Screenshots of dashboards. Exported CSVs. Manual uploads to a compliance platform. Evidence is stale before your auditor sees it.
Security and compliance are separate
Your security tools don't talk to your compliance tool. You're proving security retroactively instead of demonstrating it continuously.
Annual fire drills
Every audit cycle means weeks of prep. Your team drops everything to gather evidence, fix gaps, and chase documentation. Then it starts over.
Evidence from operations. Not from busywork.
Vimy maps controls across all five Trust Services Criteria. Evidence is generated automatically from your live security operations — every detection, every response, every posture check. Your compliance posture improves every time your security posture improves.
Common Criteria — the foundation. Access controls, incident response, risk management, change management. Vimy covers this through Identity battery monitoring, response pipeline audit trails, and posture scoring.
System uptime and performance monitoring. Vimy tracks infrastructure health, agent heartbeats, and connector status continuously.
Data processing accuracy and completeness. Vimy's OCSF normalization pipeline ensures every event is structured, validated, and queryable.
Data protection and access restrictions. Database-per-tenant isolation, field-level encryption, and role-based access control — all evidenced automatically.
Personal information handling aligned with PIPEDA. Data retention policies, consent tracking, and breach notification procedures — built into the platform.
Everything you need to get and stay SOC 2 ready.
Continuous Evidence Collection
Every security action generates compliance evidence in real time. No manual collection, no screenshot workflows, no quarterly exports.
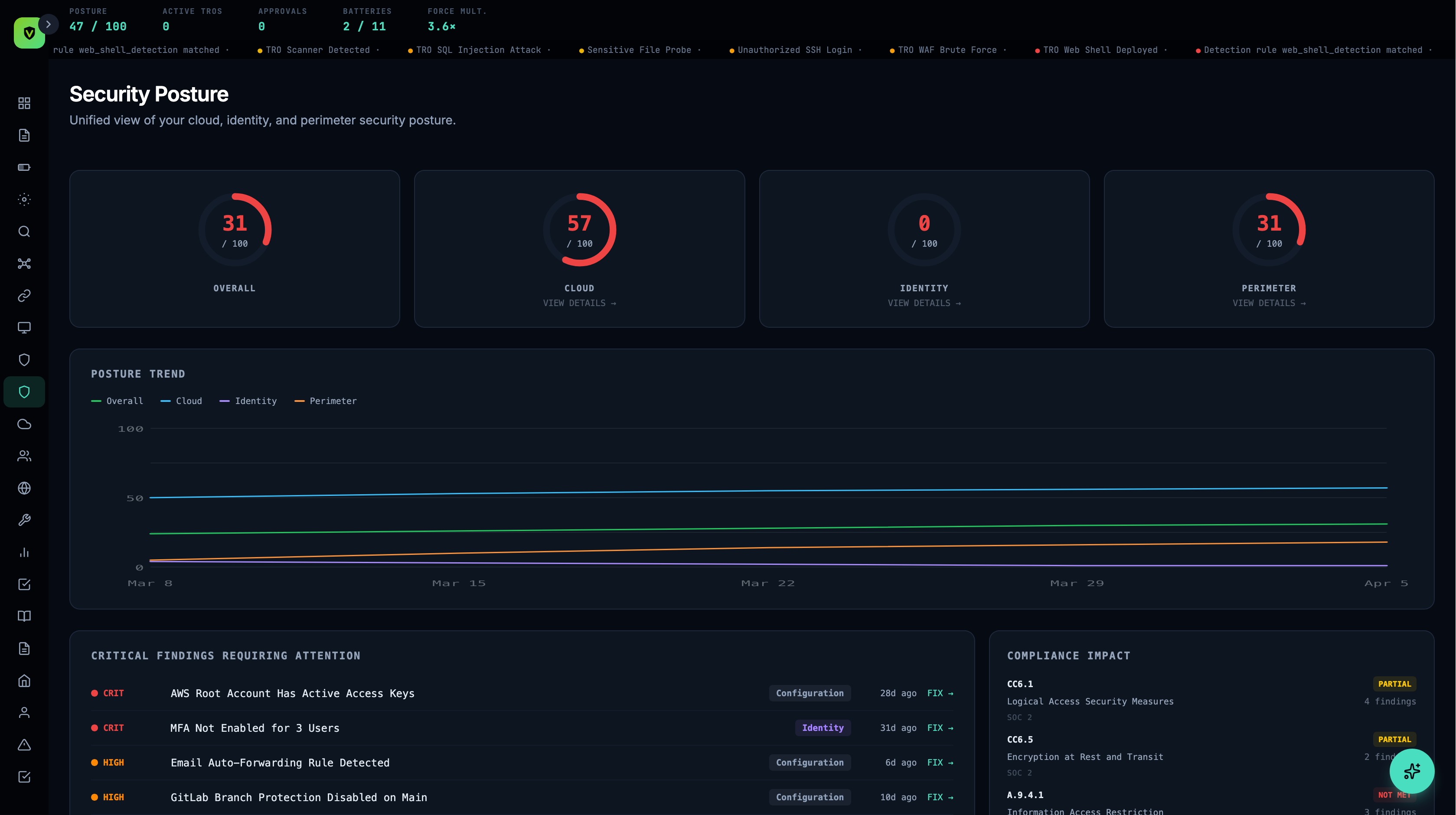
Control Mapping Dashboard
See which controls are passing, failing, or need attention. Drill into any control to see the evidence behind it and the source detection.
Auditor Portal
Generate a scoped, time-limited token for your auditor. They get read-only access to SOC 2 evidence only — no other tenant data. No manual packaging.
Trust Center
Publish your SOC 2 readiness to a public-facing page. Prospects and customers can verify your security posture without asking your team.
Gap Analysis
Vimy identifies which controls have evidence gaps and recommends which connectors or batteries to activate to close them.
Policy Templates
Pre-built security policy templates mapped to SOC 2 controls. Customize, approve, and track versions — all linked to the framework automatically.
Vimy vs. traditional SOC 2 tools.
| Traditional SOC 2 Tools | Vimy | |
|---|---|---|
| Evidence collection | Manual screenshots & uploads | Automatic from live security ops |
| Evidence freshness | Point-in-time snapshots | Continuous, real-time |
| Security integration | Separate tool, separate workflow | Security and compliance are the same system |
| Audit prep time | Weeks of manual gathering | Always audit-ready |
| Control monitoring | Periodic checks | Continuous monitoring |
| Threat detection | Not included — security is separate | +11 batteries, cross-battery correlation |
| Canadian hosting | Varies — often US-based | 100% Canadian, zero US subprocessors |
From zero to SOC 2 ready.
Connect your stack
Plug in your existing tools. Each connector immediately starts feeding evidence to SOC 2 controls.
Review your gap analysis
Vimy shows you which controls are covered, which have gaps, and what to connect next to close them.
Activate policies
Adopt policy templates, customize them to your organization, and link them to controls.
Share with your auditor
Generate an auditor portal token. Your auditor reviews evidence directly — no manual packaging required.
SOC 2 compliance features — including control mapping, auditor portal, Trust Center, and gap analysis — are available on the Bastion plan and above.
See Plans →Common questions about SOC 2 with Vimy.
See your SOC 2 readiness
in 30 minutes.
We'll connect to your environment and show you which controls light up immediately — before you commit to anything.