Perimeter Battery
Monitors your edge — the boundary between the internet and your infrastructure. Detects DDoS patterns, WAF bypass attempts, origin IP exposure, DNS hijacking, bot swarms, and SSL/TLS downgrade attacks.
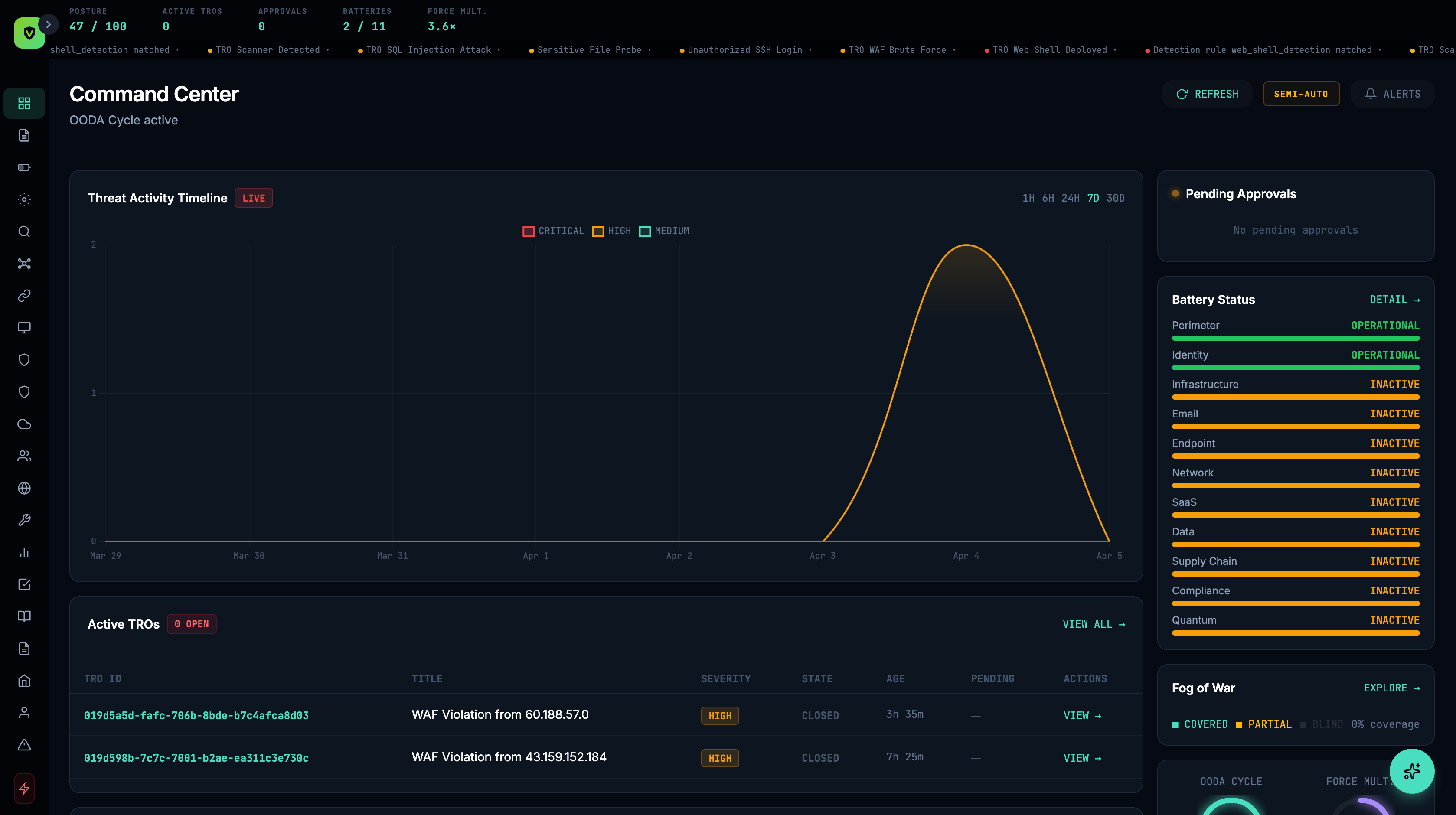
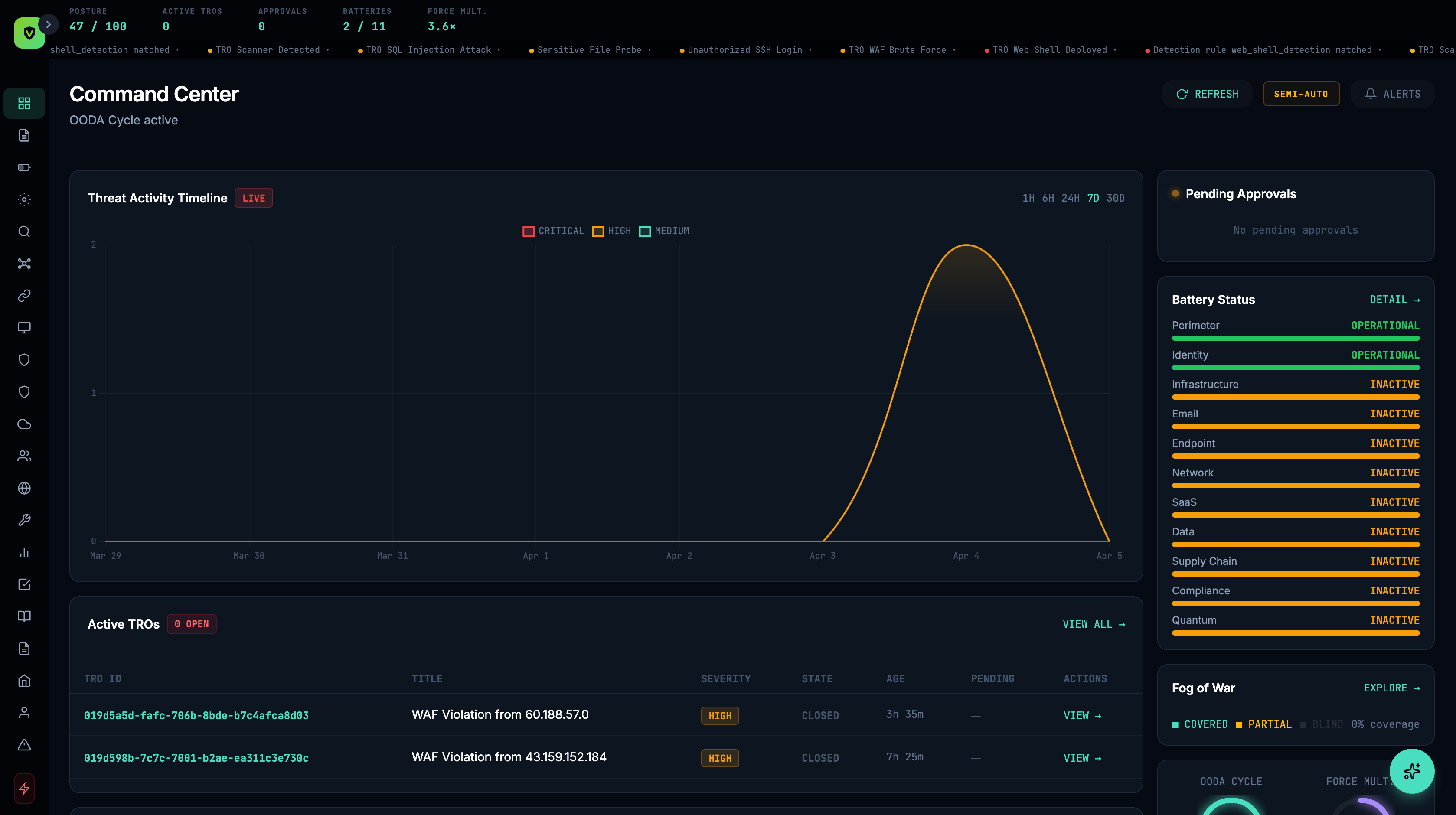
Detection SpecificationsVimy doesn't monitor one layer and hope for the best. It monitors every layer simultaneously — perimeter, identity, infrastructure, email, endpoint, network, SaaS, data, supply chain, compliance, and quantum — and correlates signals across all of them in real time.
Traditional security tools are siloed. Your EDR watches endpoints. Your SIEM aggregates logs. Your identity provider tracks logins. Each tool sees one slice — attackers move between slices.
Vimy organizes defense into batteries — a military term for coordinated defensive positions. Each battery specializes in one layer but shares intelligence with every other battery. When the Identity battery detects an impossible travel login, the Infrastructure battery is immediately on alert for that user's server access. The Perimeter battery watches for their IP across all edge traffic.
This is combined arms defense. The attacker can't evade +11 coordinated layers the way they evade one.
Cross-signal detection across your perimeter, identity, and infrastructure — with automated response.
Monitors your edge — the boundary between the internet and your infrastructure. Detects DDoS patterns, WAF bypass attempts, origin IP exposure, DNS hijacking, bot swarms, and SSL/TLS downgrade attacks.
Detection SpecificationsMonitors authentication and authorization across your identity providers. Detects account takeover, MFA bypass and fatigue attacks, OAuth abuse, impossible travel, privilege escalation, credential stuffing, and session hijacking.
Detection SpecificationsMonitors servers, cloud resources, and containerized workloads. Detects unauthorized SSH access, cryptomining, reverse shells, firewall tampering, backup deletion, SSH key injection, and API key abuse.
Detection SpecificationsVimy evaluates activity across every connected layer — matching behavior against known attack techniques, baselines, and cross-signal correlations. When something triggers, a full investigation is created automatically with evidence attached.
Learn what's normal for every user, device, and service. Flag what isn't.
Every detection ties to a known technique, so your team speaks the same language as the threat.
A login anomaly alone is noise. Paired with a firewall change? That's an attack chain.
Cross-battery correlation connects signals from different batteries into unified attack stories — catching multi-stage attacks that would appear as unrelated alerts in single-vendor tools.
A standalone email gateway sees a phishing attempt. A standalone identity tool sees an unusual login. A standalone server monitor sees an SSH session. None of them see the full attack chain. Vimy does.
The brute force, the successful auth, and the download appear in three separate tools. The correlation is the threat.
No single change is alarming. The pattern across three batteries raises the alert before exploitation begins.
When a detection fires, Vimy creates a Threat Response Operation (TRO) — a structured object with a full lifecycle. Every TRO includes a complete evidence chain, entity graph, and audit trail from detection through verified closure.
Every TRO captures the complete evidence trail — raw events, normalized data, entity relationships, detection rule that fired, AI triage reasoning, response actions taken, and verification results.
Response actions are planned as a manifest — a structured list of what will be done, to which entities, via which connectors. In supervised mode, the manifest awaits human approval before execution.
After response execution, Vimy verifies containment worked. Did the attacker adapt? Is the threat neutralized? BDA closes the loop — don't assume containment, prove it.
Vimy maps every detection specification to MITRE ATT&CK techniques. The Fog of War page in the platform shows your real-time coverage across the ATT&CK matrix — which techniques you detect, which you partially cover, and which are blind spots.
Every connector you add and every battery that activates fills in more of the matrix. Coverage is measurable, not assumed.
30-minute demo. We'll show you which layers are covered, which are exposed, and what lights up on day one.