Real-time score.
Full attack surface.
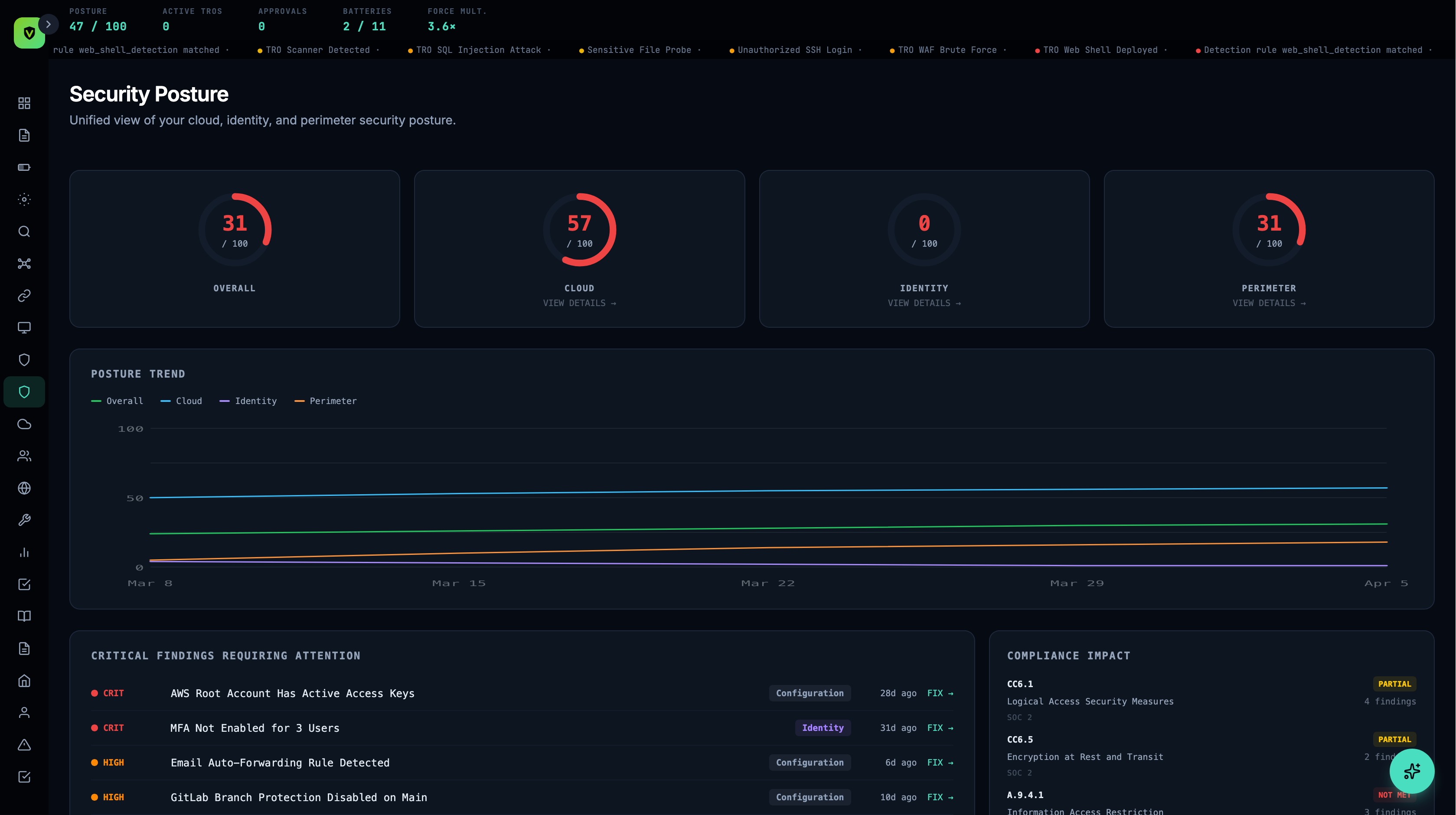
Vimy continuously measures your security posture across identity, perimeter, cloud, and endpoints — scoring your environment in real time and alerting when it drifts. Not a quarterly assessment. Not a point-in-time snapshot. A live score that reflects reality right now.
You can't secure what you can't measure.
Point-in-time assessments
Annual penetration tests and quarterly vulnerability scans give you a snapshot — but your environment changes daily. Configurations drift, new services spin up, permissions creep. The snapshot is stale before the report is printed.
No unified score
Your EDR has a health score. Your cloud provider has a security score. Your identity provider has a risk score. None of them talk to each other. You have five numbers and no answer to "are we secure?"
Reactive, not proactive
Most security tools wait for something bad to happen. Posture monitoring catches the conditions that lead to something bad — misconfigurations, weak settings, exposed services, stale credentials — before they're exploited.
One number. Every layer.
Vimy calculates a unified posture score from 0 to 100 by aggregating security health across every connected layer. The score updates in real time as your environment changes — configurations, permissions, policies, and compliance controls all feed into a single, actionable number.
Scores shown are illustrative. Your posture score is calculated from your actual environment.
Every angle of your attack surface. Measured.
Identity Posture
Monitors how well your identity infrastructure is configured and maintained. Tracks MFA enforcement rates, password policy strength, OAuth app permissions, inactive accounts, admin privilege sprawl, and session management settings.
Key Checks- MFA enforcement across all users
- OAuth apps with excessive permissions
- Stale accounts not accessed in 90+ days
- Admin accounts without MFA
- Password policy strength
Perimeter Posture
Monitors the security configuration of your edge — the boundary between the internet and your infrastructure. Tracks WAF ruleset coverage, SSL/TLS configuration, DNS security settings, origin IP protection, and bot management effectiveness.
Key Checks- WAF managed rulesets enabled and updated
- TLS 1.2+ enforced, TLS 1.3 preferred
- DNSSEC enabled
- Origin IP not exposed
- Bot Fight Mode active
Cloud Security
Monitors the security configuration of your cloud infrastructure. Tracks firewall rules, storage bucket permissions, API key rotation, resource tagging compliance, backup configuration, and network segmentation.
Key Checks- Firewall rules reviewed and minimal
- No public storage buckets
- API keys rotated within policy
- Backups configured and verified
- Logging enabled on all resources
Hardening
Monitors the configuration of individual servers and endpoints against security baselines. Tracks OS hardening, unnecessary service exposure, patch status, encryption settings, and logging coverage.
Key Checks- SSH key-only authentication
- Unnecessary ports closed
- Automatic security updates enabled
- Disk encryption active
- Audit logging configured
Catch changes before they become vulnerabilities.
Security posture degrades over time. Configurations get changed during debugging and never reverted. New team members get admin access "temporarily." Firewall rules accumulate exceptions. Vimy detects these drifts automatically and alerts before they become exploitable.
Drift detection runs continuously — not on a schedule. The moment a configuration changes in a way that weakens your posture, Vimy flags it.
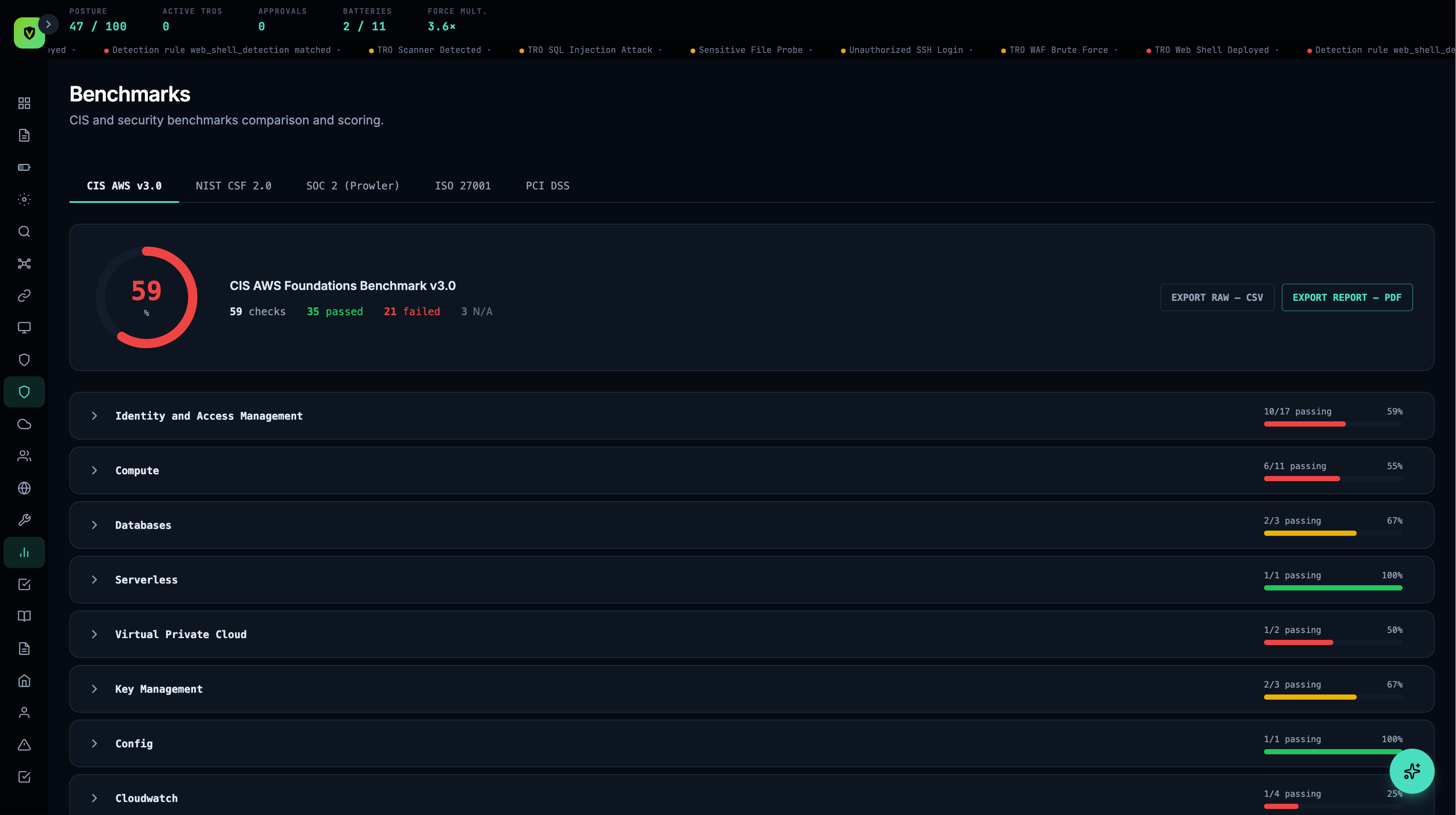
Industry benchmarks. Continuously tested.
Vimy runs your environment against industry-standard benchmarks — CIS Controls v8 and NIST CSF 2.0 — continuously. Not a one-time scan, not an annual audit. Every benchmark check runs against your live configuration and updates your benchmark score in real time.
18 Critical Security Controls across three Implementation Groups (IG1, IG2, IG3). Vimy tracks your implementation level for each control and collects evidence continuously.
Six core functions — Identify, Protect, Detect, Respond, Recover, Govern. Vimy maps security operations to each function and provides a function-level maturity score.
Benchmark results feed into your compliance posture. CIS and NIST evidence automatically satisfies overlapping controls in SOC 2, ISO 27001, and other frameworks.
Every posture check is compliance evidence.
When Vimy checks your MFA enforcement rate, that check satisfies posture scoring and maps to SOC 2, ISO 27001, and NIST CSF simultaneously. One check, multiple frameworks, zero duplicate work.
Your posture score and your compliance score are two views of the same data. Improve one, and the other improves automatically.
See Compliance Automation →Trends your leadership can track.
Vimy generates posture reports automatically — weekly summaries, monthly trends, and on-demand snapshots. See your score over time, identify recurring drift patterns, and demonstrate continuous improvement to leadership, auditors, and cyber insurers.
See your posture score in 30 minutes.
We'll connect to your environment and calculate your real-time posture score — across identity, perimeter, cloud, and hardening — live on the call.