ISO 27001 compliance without a separate ISMS project.
Vimy maps controls across Annex A and continuously evidences your information security management system from live security operations. No consultants. No parallel workstreams.
ISO 27001 is powerful. Getting there shouldn't be painful.
ISO 27001 is the global gold standard for information security management. But implementing an ISMS from scratch typically means 6–12 months of consulting, policy writing, risk assessments, and evidence gathering — often in a completely separate system from your actual security operations.
By the time you reach certification, the evidence is already stale and the cycle starts over for your surveillance audit.
ISMS as a parallel project
Most organizations build their ISMS in a GRC tool that's disconnected from their security stack. Evidence is imported, not generated.
Annex A mapping is manual
Mapping technical controls to Annex A requirements is tedious, subjective, and rarely kept up to date after the initial certification push.
Surveillance audits reset the clock
Annual surveillance audits mean annual evidence gathering sprints. Continuous compliance is the goal — but without automation, it's just a slogan.
Your ISMS, built from real security data.
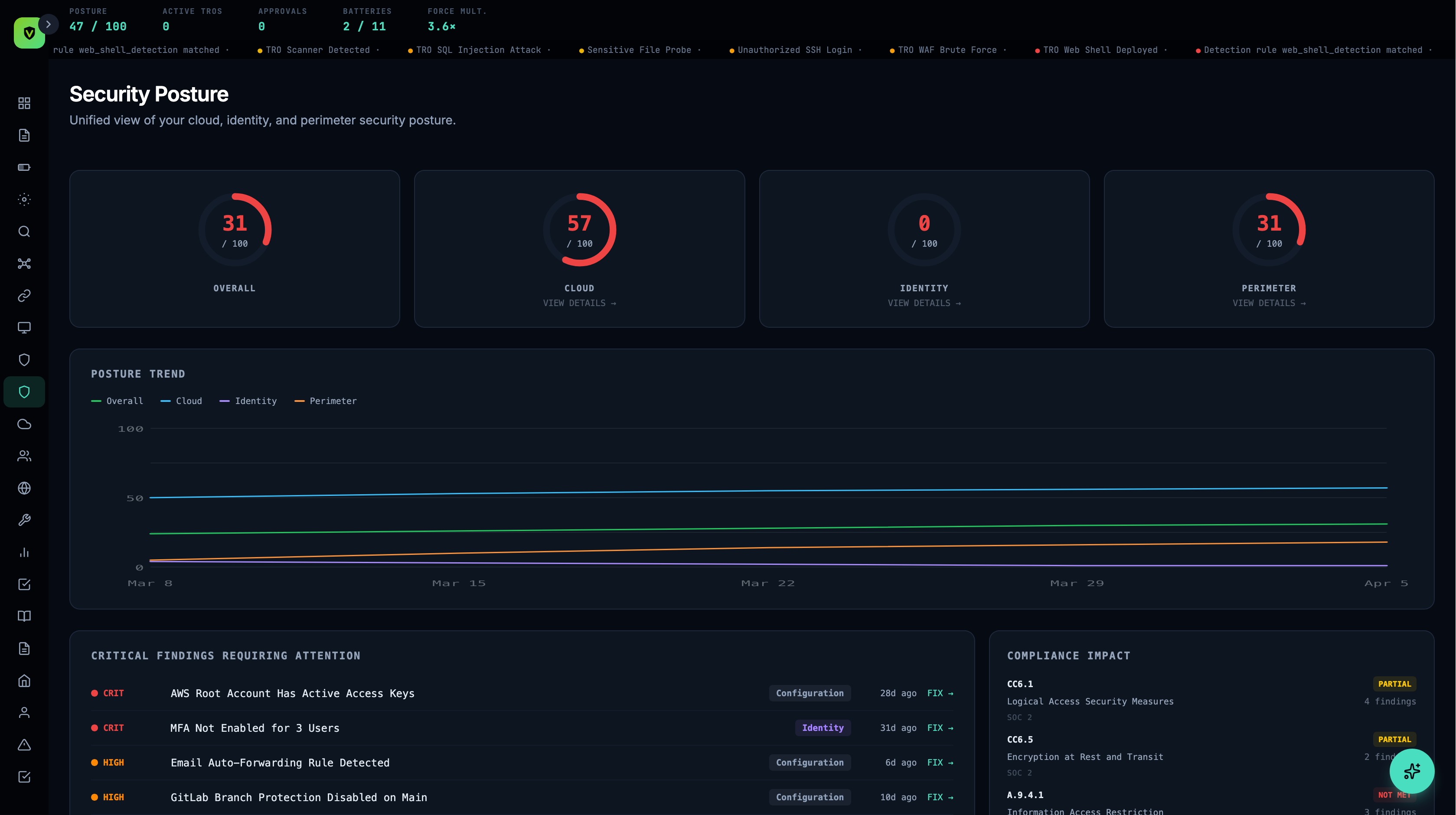
Vimy maps controls across the Annex A domains. Every security detection, response action, posture check, and policy approval generates evidence against your ISMS requirements automatically. Your information security management system isn't a separate project — it's the natural output of running Vimy.
Information security policies, roles, responsibilities, and management direction. Policy management and approval workflows built directly into Vimy.
Screening, awareness, training records, and access reviews. People management and training tracking in the Compliance section.
Access control, cryptography, operations security, network security. This is where Vimy's +11 batteries directly map — every detection and response is Annex A evidence.
Physical security is primarily your responsibility, but Vimy tracks related policies and evidences cloud infrastructure controls that replace traditional physical requirements.
From gap analysis to surveillance audit — covered.
Annex A Control Mapping
Controls mapped to Vimy's security batteries, connectors, and compliance features. See which controls are passing, failing, or need attention — in real time.
Statement of Applicability
Generate your Statement of Applicability directly from Vimy's control mapping. Include justifications for excluded controls with full version history.
Risk Register
Track information security risks with severity, likelihood, treatment plans, and residual risk scores. Link risks directly to Annex A controls for full traceability.
Continuous ISMS Evidence
Every security action maps to ISMS requirements automatically. Your evidence is never stale — surveillance auditors see live data, not a point-in-time snapshot.
Auditor Portal
Give your certification body scoped, read-only access to ISO 27001 evidence. Time-limited tokens, framework-filtered views — no manual packaging required.
Policy Management
ISO 27001-aligned policy templates with version tracking, approval workflows, and automatic control mapping. Review cycles managed in-platform.
SOC 2 and ISO 27001. Same data. Same platform.
Many organizations need both SOC 2 (for North American customers) and ISO 27001 (for international customers and regulatory requirements). With traditional tools, that means two separate compliance projects mapping to the same security controls. Vimy maps both simultaneously. A single security event can satisfy controls in SOC 2, ISO 27001, NIST CSF, and more — at the same time. No duplicate work.
from Vimy
Plus NIST CSF, PIPEDA, Law 25, CIS Controls, and CPCSC — all from the same security data. See all frameworks →
From zero to ISMS.
Connect your infrastructure
Plug in your existing security tools. Each connector feeds evidence to Annex A controls immediately.
Review gap analysis
Vimy identifies which Annex A controls are covered, partially covered, or missing. Your Statement of Applicability starts taking shape.
Adopt policies and treat risks
Use ISO 27001-aligned policy templates. Document risk treatments in the risk register. Fill the gaps identified in step 2.
Certify with confidence
Your auditor accesses evidence directly through the auditor portal. Surveillance audits become routine — evidence is always current.
ISO 27001 compliance features — including Annex A mapping, risk register, Statement of Applicability, and auditor portal — are available on the Bastion plan and above.
See Plans →Common questions about ISO 27001 with Vimy.
See your Annex A coverage
in 30 minutes.
We'll connect to your environment and show you which ISO 27001 controls light up immediately.